CountLoader Malware
Cybersecurity analysts have uncovered a fresh malware distribution campaign that abuses websites offering pirated software to spread an updated variant of a covert, modular loader known as CountLoader. By preying on users searching for cracked applications, the operators gain an initial foothold that enables stealthy access, defense evasion, and the staged delivery of additional malicious tools.
Table of Contents
CountLoader’s Role in a Multi-Stage Intrusion
In this campaign, CountLoader functions as the first component in a broader attack chain. Earlier investigations had already shown the loader's ability to deploy a range of secondary payloads, including Cobalt Strike, AdaptixC2, PureHVNC RAT, Amatera Stealer, and PureMiner. Evidence suggests that CountLoader has been actively used in real-world attacks since at least June 2025, underscoring its maturity and continued development.
From Fake Downloads to Silent Execution
The infection sequence starts when victims attempt to download cracked versions of legitimate software such as Microsoft Word. Instead of receiving the promised application, they are redirected to a MediaFire-hosted ZIP archive. This archive contains two key items: an encrypted ZIP file and a Word document that conveniently supplies the password needed to open it.
Inside the protected archive is a legitimate Python interpreter that has been renamed to Setup.exe. This executable is configured to launch a malicious command that leverages mshta.exe to retrieve CountLoader version 3.2 from a remote server, quietly initiating the compromise.
Persistence Through Deception and Environment Awareness
To ensure long-term access, the malware establishes persistence by creating a scheduled task designed to look legitimate. It adopts the name 'GoogleTaskSystem136.0.7023.12' followed by a string resembling a unique identifier. This task is configured to execute every 30 minutes for a decade, invoking mshta.exe and relying on a fallback domain if needed.
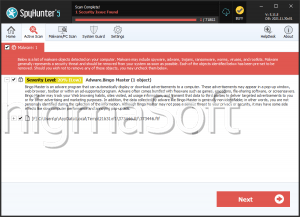
Before finalizing its persistence mechanism, CountLoader checks the system for the presence of a specific security product by querying the antivirus inventory through Windows Management Instrumentation (WMI). If the tool is detected, the loader subtly alters its execution method to use cmd.exe /c start /b mshta.exe . If not, it directly contacts the remote URL using mshta.exe, minimizing friction and suspicion.
Expanding Capabilities and Modular Features
Once established, CountLoader profiles the infected host and retrieves additional payloads as required. The latest iteration introduces new functionality, including the ability to spread through removable USB drives and to execute malicious code directly in memory using mshta.exe or PowerShell. Its supported capabilities include:
- Retrieving and running executables from remote URLs
- Downloading ZIP archives and executing embedded Python modules or EXE files
- Fetching DLL files and launching them via rundll32.exe
- Downloading and installing MSI packages
- Removing its own scheduled task to reduce forensic traces
- Collecting and exfiltrating detailed system information
- Propagating through removable media by creating malicious LNK files alongside hidden originals, which execute both the legitimate file and the malware via mshta.exe with Command-and-Control parameters
- Directly invoking mshta.exe against attacker-controlled URLs
- Executing remote PowerShell payloads entirely in memory
The Final Payload: ACR Stealer
In the observed attack chain, CountLoader ultimately delivered ACR Stealer, an information-stealing malware designed to siphon sensitive data from compromised systems. This final stage transforms an initial lure involving pirated software into a full-scale data theft operation.
What This Campaign Signals for Defenders
This operation demonstrates CountLoader's continued evolution and growing sophistication. The combination of Python interpreter abuse, scheduled task masquerading, signed binary misuse, and fileless, in-memory execution reflects a broader shift toward stealthier intrusion techniques. For defenders, the campaign reinforces the importance of proactive monitoring, layered security controls, and user awareness, especially around the risks of downloading unauthorized or cracked software.